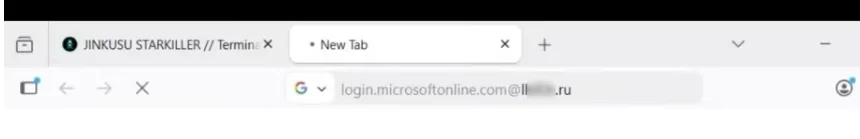
‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA
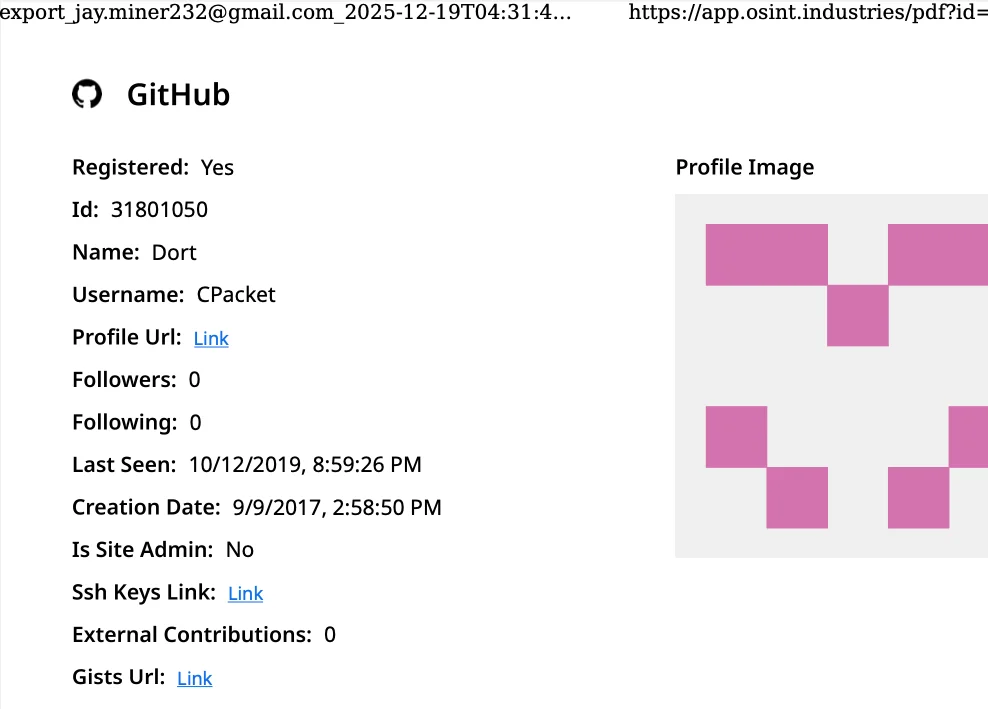
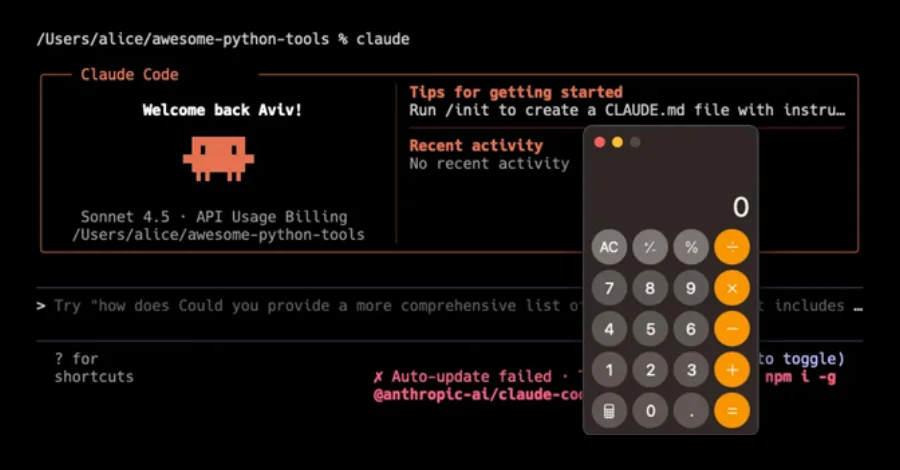
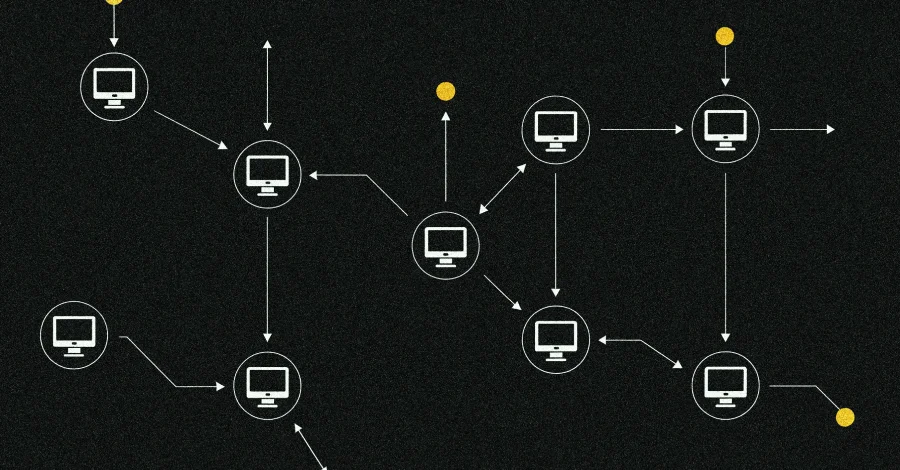
Most phishing websites are little more than static copies of login pages for popular online destinations, and they are often quickly taken down by anti-abuse activists and security firms. But a stealt...