
GLiNER2: Unified Schema-Based Information Extraction
Article URL: https://github.com/fastino-ai/GLiNER2 Comments URL: https://news.ycombinator.com/item?id=47266736 Points: 44 # Comments: 3
Programming languages, frameworks, and development tools
Found 82 articles

Article URL: https://github.com/fastino-ai/GLiNER2 Comments URL: https://news.ycombinator.com/item?id=47266736 Points: 44 # Comments: 3

Biggest comeback of 2026.
Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments surfaced over the past few days, showing how quickly the threat landscape keeps shifting. Researchers unc...

Mint's been holding back for good reason, but here we are!
From interoperability to knowledge architecture to creating AI tools people can actually use, here’s a recap of what we learned from DeveloperWeek 2026.

Article URL: https://grith.ai/blog/clinejection-when-your-ai-tool-installs-another Comments URL: https://news.ycombinator.com/item?id=47263595 Points: 345 # Comments: 80
Article URL: https://lucumr.pocoo.org/2026/3/5/theseus/ Comments URL: https://news.ycombinator.com/item?id=47263048 Points: 60 # Comments: 65
Project initiated by Nuxt lead Daniel Roe attracts wide support thanks to multiple issues with the official interface A new browser for the npm registry has launched in alpha, following grassroots dem...
We’re not getting smarter with AI — we’re just getting better at hoarding prompts and calling it “creativity.” The real danger isn’t AI replacing us. It’s us quietly forgetting how to think.
Geopolitical tensions turn up the pressure for European legislators The UK is still in the design phase of digital currency as the EU comes under political pressure to accelerate the development of a ...
Survey of UK bosses find 62 percent rely on LLMs for help Most business leaders in the United Kingdom appear to have outsourced a lot of their decisionmaking to machine learning models, according to a...
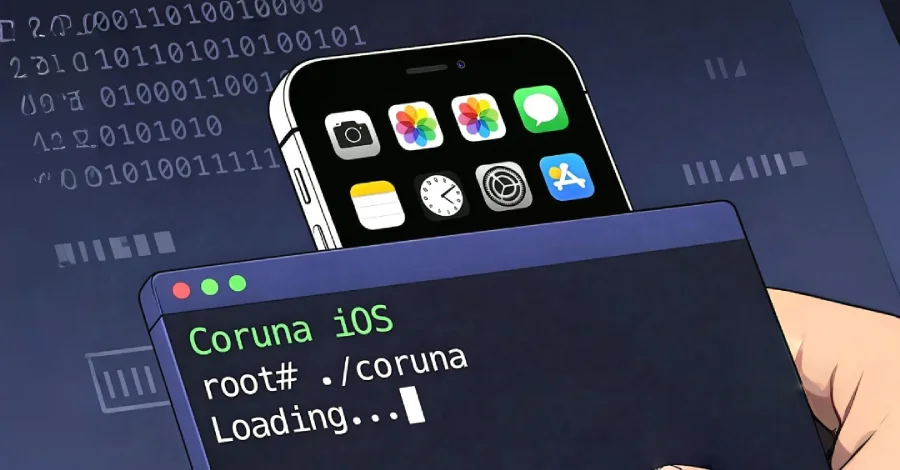
Google said it identified a "new and powerful" exploit kit dubbed Coruna (aka CryptoWaters) targeting Apple iPhone models running iOS versions between 13.0 and 17.2.1. The exploit kit featured five fu...
Cybersecurity researchers have flagged malicious Packagist PHP packages masquerading as Laravel utilities that act as a conduit for a cross-platform remote access trojan (RAT) that's functional on Win...

This past week, I’ve been deep in the trenches helping customers transform their businesses through AI-DLC (AI-Driven Lifecycle) workshops. Throughout 2026, I’ve had the privilege of facilitating thes...
Product thinking shifts your focus from "how it looks" to "why it matters," ensuring every design choice solves a real human problem and hits a business goal. It’s the secret to moving beyond pixel-pu...
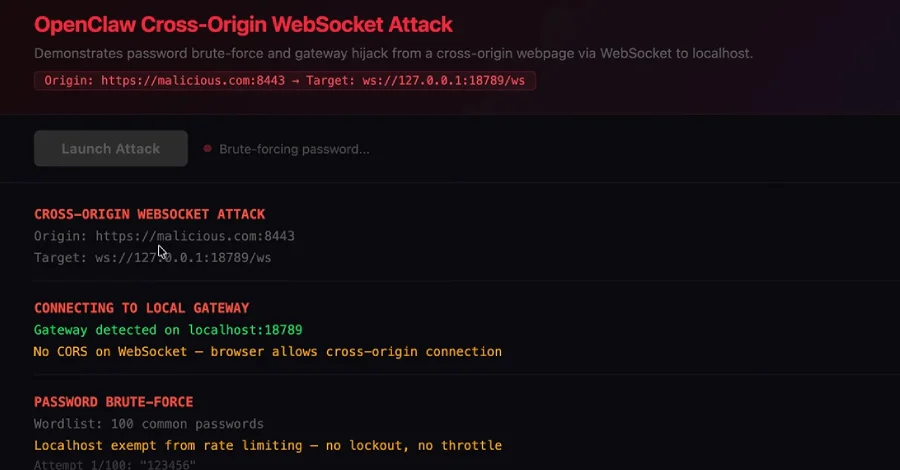
OpenClaw has fixed a high-severity security issue that, if successfully exploited, could have allowed a malicious website to connect to a locally running artificial intelligence (AI) agent and take ov...

New research has found that Google Cloud API keys, typically designated as project identifiers for billing purposes, could be abused to authenticate to sensitive Gemini endpoints and access private da...
Ryan welcomes Marcus Fontoura, technical fellow at Microsoft and author of Human Agency in the Digital World, to discuss the intersection of technology, society, and human dignity in a digital-first w...
A description of some of the recent changes to do allocations on the stack instead of the heap.
A "coordinated developer-targeting campaign" is using malicious repositories disguised as legitimate Next.js projects and technical assessments to trick victims into executing them and establish persi...