Design for Safety, An Excerpt
Antiracist economist Kim Crayton says that “intention without strategy is chaos.” We’ve discussed how our biases, assumptions, and inattention toward marginalized and vulnerable groups lead to dangero...
Cybersecurity threats, protection strategies, and best practices
Found 84 articles
Antiracist economist Kim Crayton says that “intention without strategy is chaos.” We’ve discussed how our biases, assumptions, and inattention toward marginalized and vulnerable groups lead to dangero...
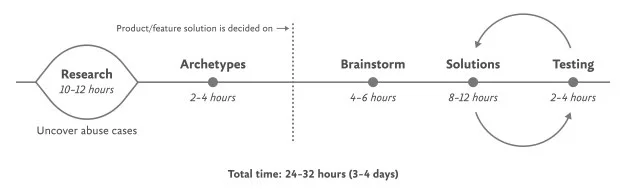
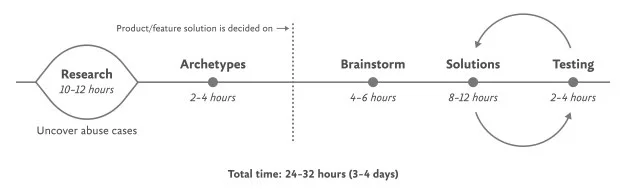
About two and a half years ago, I introduced the idea of daily ethical design. It was born out of my frustration with the many obstacles to achieving design that’s usable and equitable; protects peopl...
As a product builder over too many years to mention, I've lost count of the number of times I've seen promising ideas go from zero to hero in a few weeks, only to fizzle out within months. Financial p...
Article URL: https://www.anthropic.com/news/where-stand-department-war Comments URL: https://news.ycombinator.com/item?id=47269263 Points: 231 # Comments: 192
Of the 90 zero-days GTIG tracked in 2025, 43 hit enterprise tech Zero-day exploitation targeting enterprise tech products reached an all-time high last year, with China-linked cyber-espionage groups r...

I sure ain't opposed to some distro hopping.

Another AI hallucination went viral
Article URL: https://m4iler.cloud/posts/lets-get-physical/ Comments URL: https://news.ycombinator.com/item?id=47266030 Points: 109 # Comments: 15
Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments surfaced over the past few days, showing how quickly the threat landscape keeps shifting. Researchers unc...

Mint's been holding back for good reason, but here we are!
MOIS-linked MuddyWater crew has a new, custom implant An Iranian cyber crew believed to be part of the Iranian Ministry of Intelligence and Security (MOIS) has been embedded in multiple US companies' ...
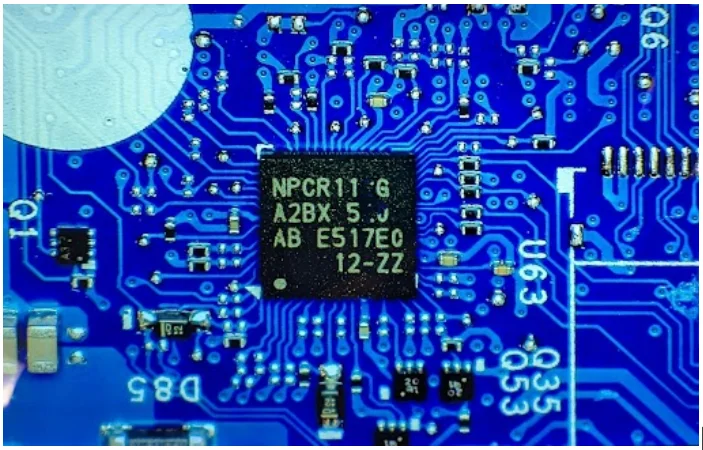
Article URL: https://opensource.googleblog.com/2026/03/opentitan-shipping-in-production.html Comments URL: https://news.ycombinator.com/item?id=47265619 Points: 87 # Comments: 12

Article URL: https://jyn.dev/remotely-unlocking-an-encrypted-hard-disk/ Comments URL: https://news.ycombinator.com/item?id=47265521 Points: 98 # Comments: 52

Google Street View can show more than you want it to.
LibreOffice steward says Commish undermines its own standards by asking for feedback via Excel spreadsheet The Document Foundation has taken a swipe at the European Commission over its consultation on...

A suspected Iran-nexus threat actor has been attributed to a campaign targeting government officials in Iraq by impersonating the country's Ministry of Foreign Affairs to deliver a set of never-before...

Nothing's Phone 4a Pro may look like the more exciting option next to the Pixel 10a, but a closer look reveals why Google's mid-ranger still is the more sensible choice. The post The Nothing Phone 4a ...

Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are no longer enough to access systems. In Windows environments, that assumption is often wrong. Attacker...

Article URL: https://grith.ai/blog/clinejection-when-your-ai-tool-installs-another Comments URL: https://news.ycombinator.com/item?id=47263595 Points: 345 # Comments: 80
Cybersecurity researchers have disclosed details of a new Russian cyber campaign that has targeted Ukrainian entities with two previously undocumented malware families named BadPaw and MeowMeow. "The ...